Authentication to NIS | Windows And Linux Integration Hands-on Solutions for a Mixed Environment - 2005 publication.
1 Network Information System (NIS). 2 Module – Network Information System ( NIS) ♢ Overview This module focuses on configuring and managing Network Information. - ppt download

A STANDALONE SAMBA-NIS/NFS SERVER MODEL FOR WINDOWS AND LINUX DUAL BOOT CLIENTS WITH INDIVIDUAL USER AUTHENTICATION | Semantic Scholar
14.1 Sun's Network Information Service (NIS) :: Chapter 14. Network-Based Authentication Systems :: Part III: Network and Internet Security :: Ppractical unix & internet security :: Linux systems :: eTutorials.org

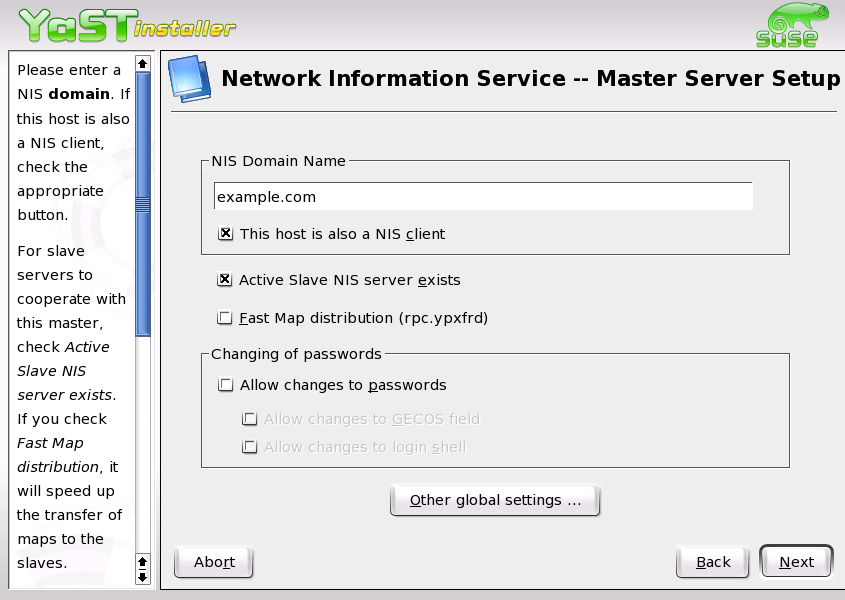
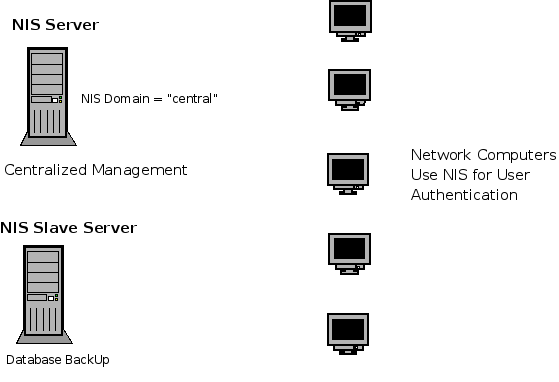
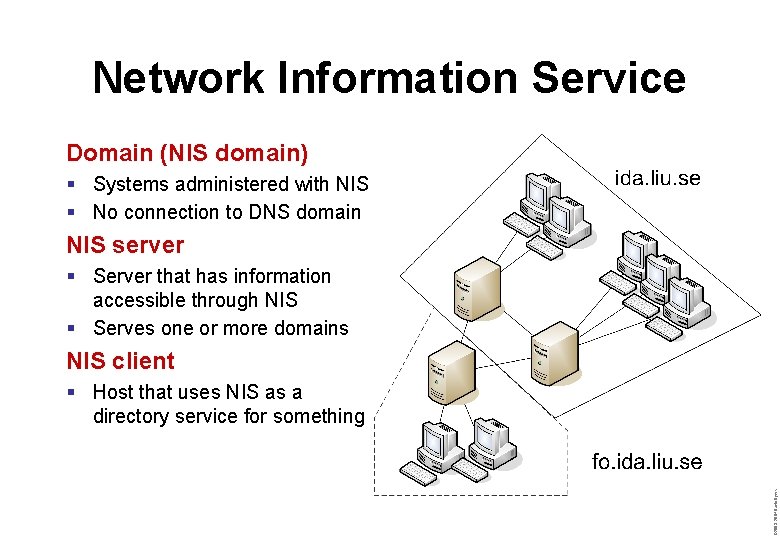
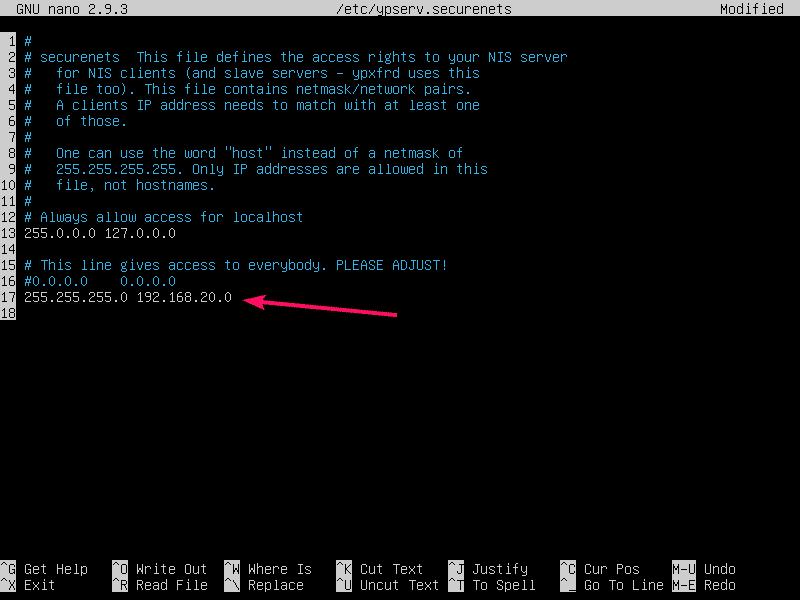
Data sharing over NIS The system configuration files (data) are maintained and stored on the NIS server in centralized way. The NIS clients bind to the NIS server and quiry the data. Previous Page previous First Page top Next Page next


![Network Information System [Client Networking] Network Information System [Client Networking]](https://www.distributednetworks.com/redhat-linux-admin/module7/images/nis3.gif)
![Chapter 19] 19.4 Sun's Network Information Service (NIS) Chapter 19] 19.4 Sun's Network Information Service (NIS)](http://litux.nl/Books/Books/www.leothreads.com/e-book/oreillybookself/tcpip/puis/figs/puis_1901.gif)