Optimizing Your Nmap Scan: Nmap Scanning Methods - Professor Messer IT Certification Training Courses

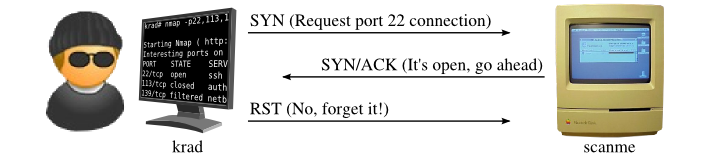
Nmap Network Scanning: The Official Nmap Project Guide to Network Discovery and Security Scanning: 8601404706585: Computer Science Books @ Amazon.com

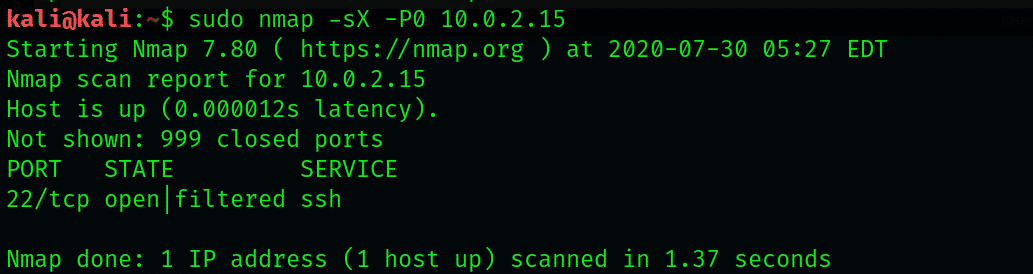
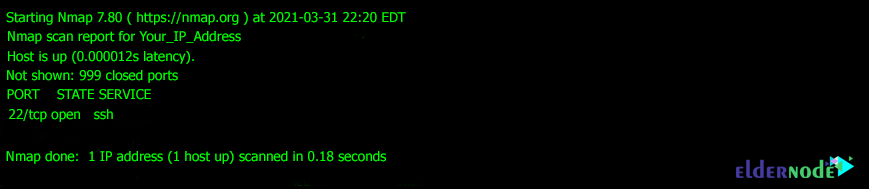
David Bombal on Twitter: "Your First Nmap Scan #nmap #network #scanner #tool #portscanner #hacking #hacker #hackingtools #cybersecurity #scanning # scan #port #portscanning #gathering #cyber #security https://t.co/IRDK5u8AML" / Twitter
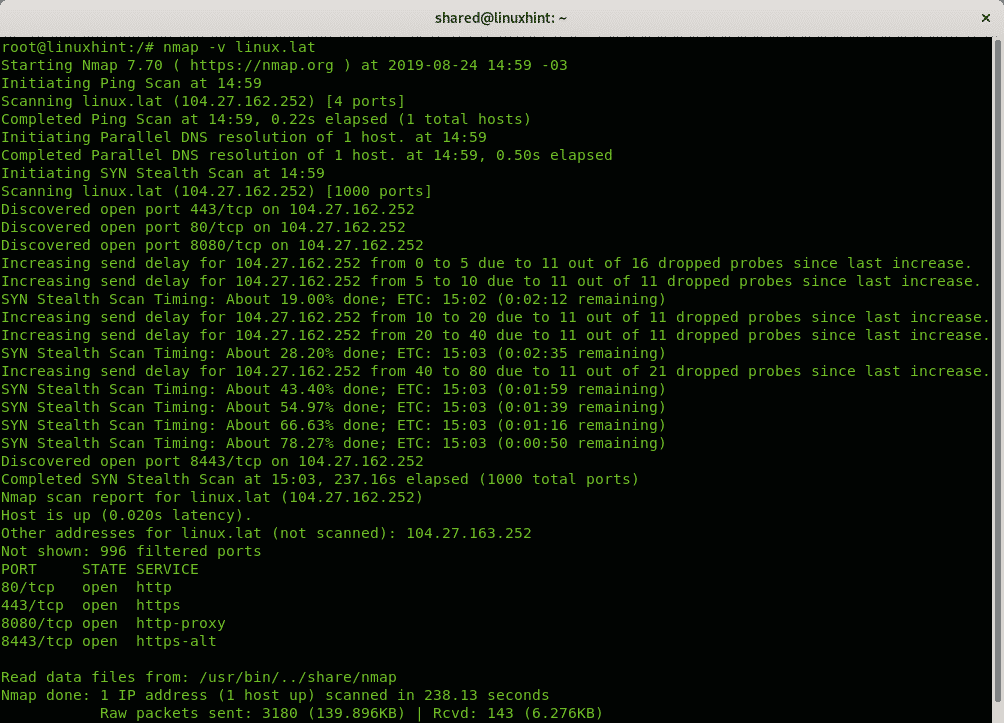
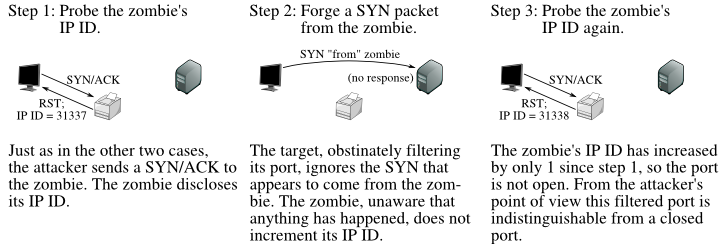
Optimizing Your Nmap Scan: Nmap Scanning Methods - Professor Messer IT Certification Training Courses