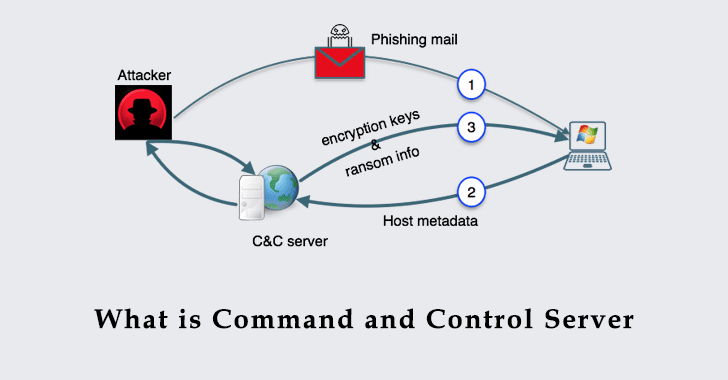
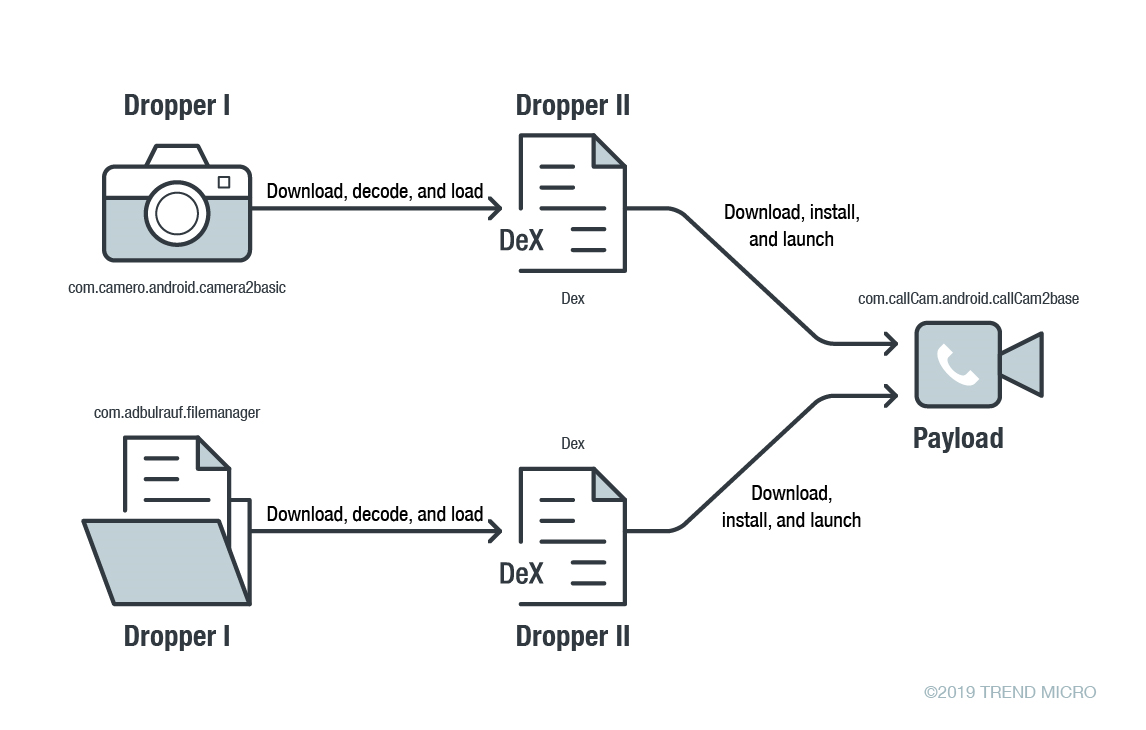
Malware hides C&C server communications using Google Docs function - Security AffairsSecurity Affairs
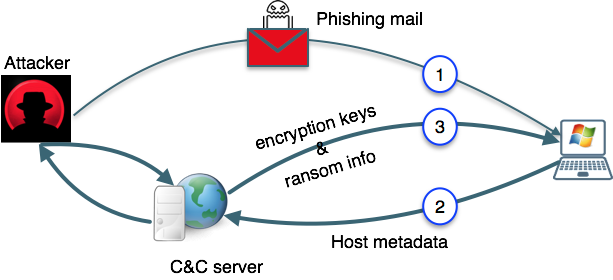
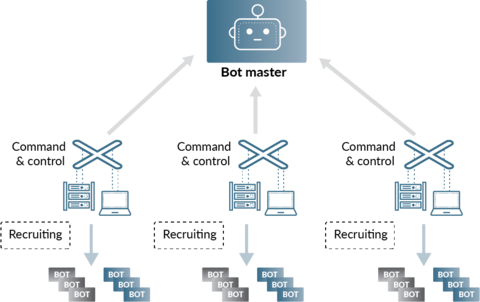
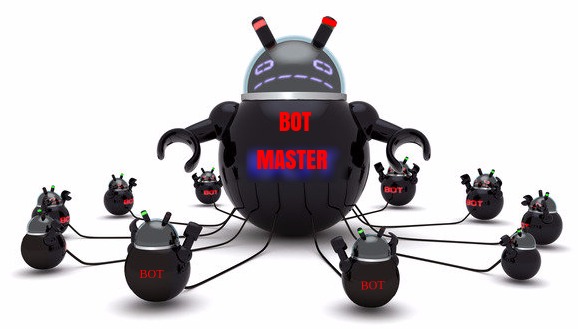
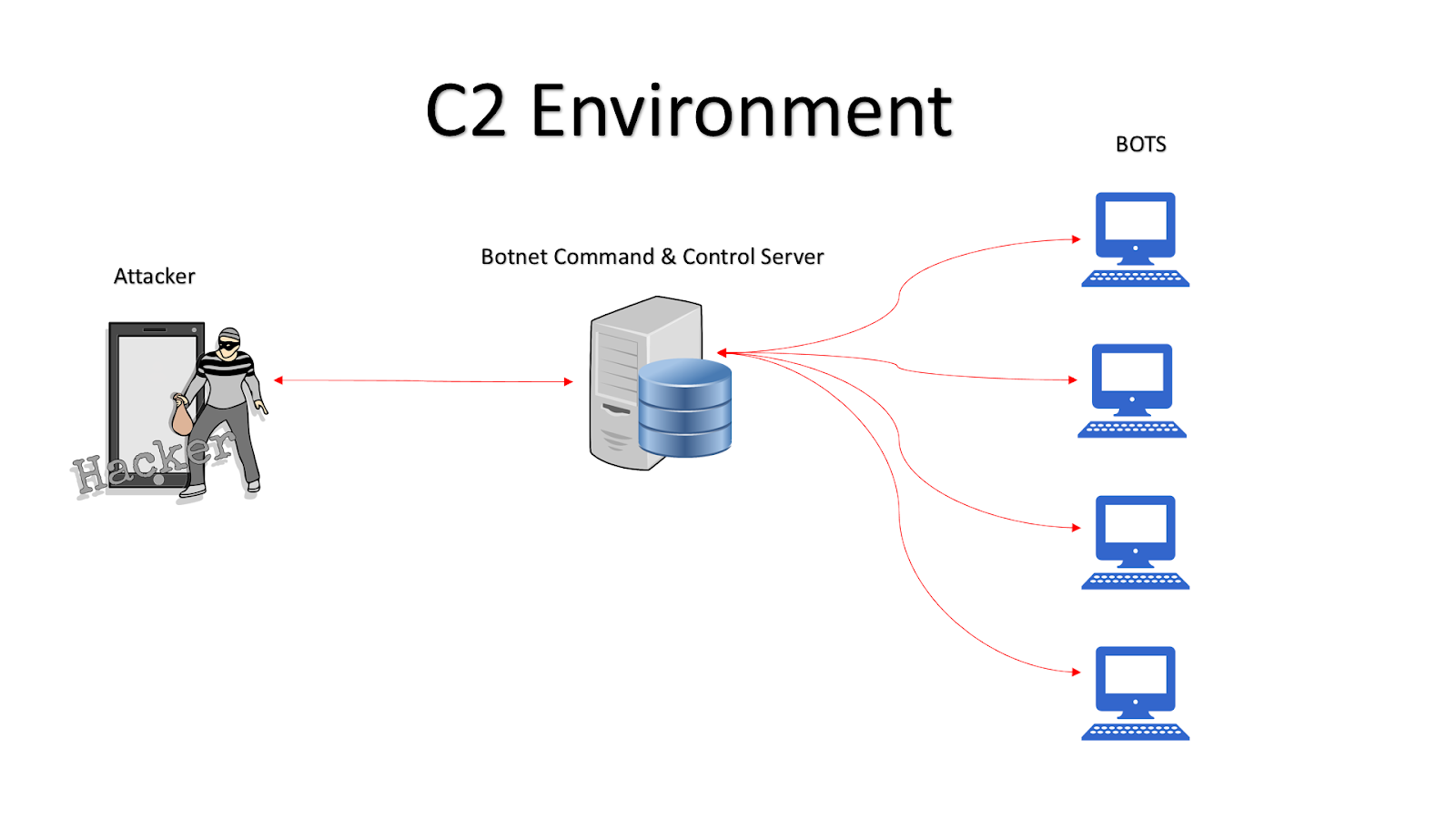
Basic entities of botnet: bots, command and control (C&C) server, and... | Download Scientific Diagram

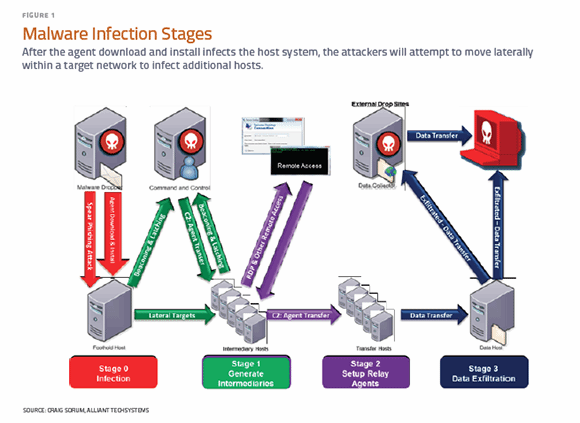
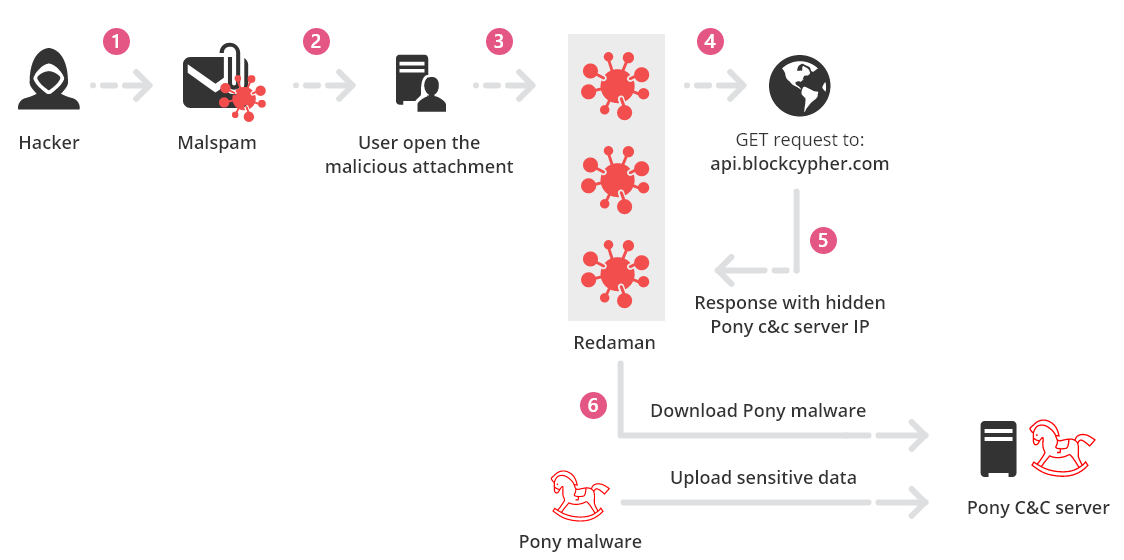
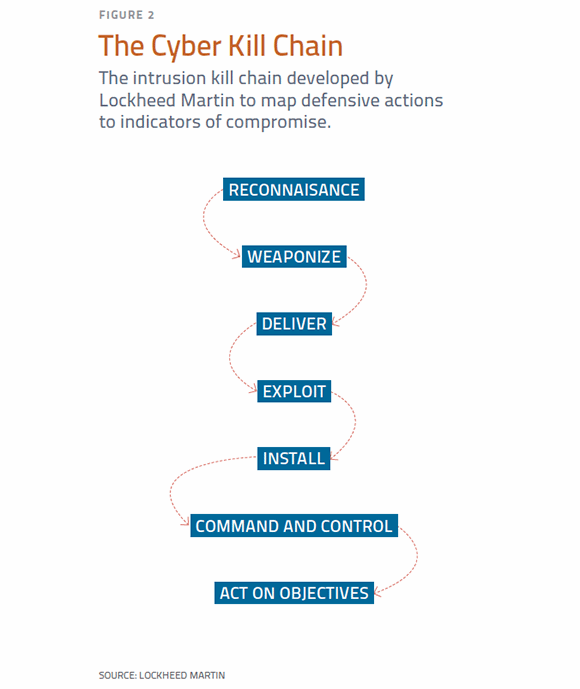
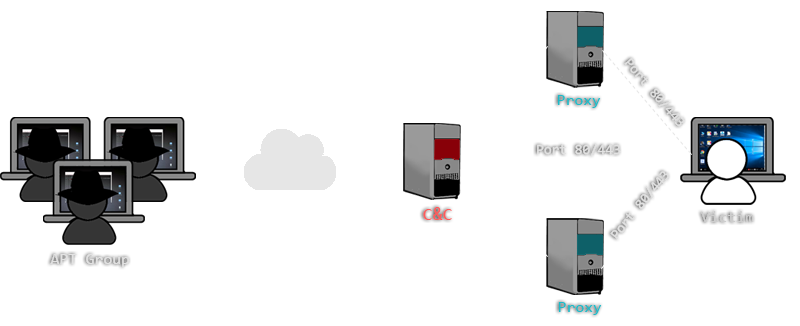
Obtain C&C Channel. Command and Control is a key role to… | by Mohans | Redteam & Blueteam Series | Medium